Safe repository. Hack SVN (GIT hack)
If you are using for your website any repository system, beware how you do deploy the web.
A simple example of the abuse
(a example for SVN system – works the same for GIT)
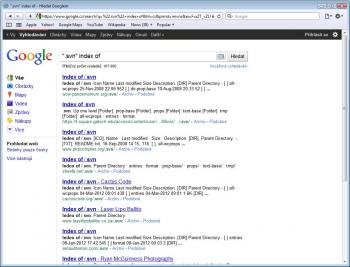
1. open google and search for the:
Objective-C
|
1 |
".svn" index of |
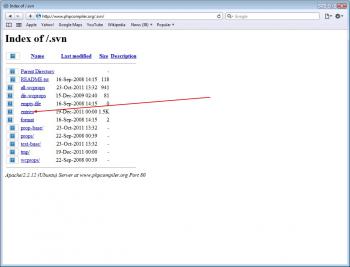
2. open any link and find the file with name “entries”
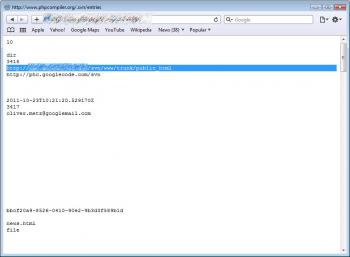
3. found in the file path to the repository
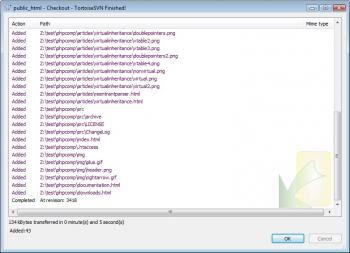
4. open your SVN client and download this repository
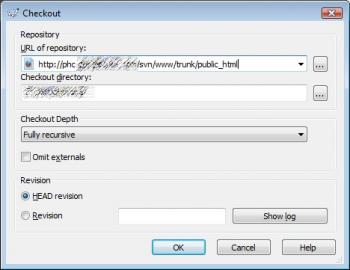
5. you have the entire contents of the repository
Of course, the repository can be password-protected or otherwise secured, but also in this case it is a risk.
Securing Apache
Server settings:
Objective-C
|
1 2 3 4 |
<DirectoryMatch ./svn> Order allow, deny Deny from all </DirectoryMatch> |
Generates a 403 Forbidden page, and will not allow viewing svn directory structure.
Alternatively, you can disable this in the htaccess file:
Objective-C
|
1 2 3 4 5 6 |
RewriteEngine On RewriteRule /.svn /some-non-existant-404-causing-page <IfModule autoindex_module> IndexIgnore .svn </IfModule> |
Result
The best solution is delete a .svn directories to the public or not copy at public webspace.
Posted on 8 November 2012
